The outcomes of OT systems are rigid and set in stone. They won’t be as adaptable as their IT counterparts because they were built to do one thing and one thing only. An increasing number of assaults are being made against these systems because of the vulnerabilities created by the difficulties of controlling expanding and farther networked setups. This is why protecting industrial networks with operational technology cybersecurity is becoming crucial.
What Does “OT” Stand For In “OT Security?”
What follows is a brief definition and overview of operational technology cybersecurity, followed by an analysis of its significance. If you’re already familiar with OT cyber security and want to go on to the next section, you may do so by clicking here.
How come protecting our operational technologies is essential?
- Prioritising system stability over data security has led several businesses to forego updating their OT systems. Without them, the factory risks losing valuable real-time data and falling behind on its production plans, so it’s critical that they’re always running smoothly.
- Delays or unscheduled outages can cost a company time and money, which is why some OT systems are allowed to continue in their existing form. Nonetheless, this indicates that machines in factories around the world may be operating with minimal security, and that these machines will be increasingly interconnected. Here is where most of the security worries are concentrated.
- Attackers looking for exploits and entry points into industrial networks will find these vulnerabilities enticing. Because of the real-world consequences of a breach, such as a tripped breaker that turns off the power, OT security is of the utmost importance.
- There has been a rise in the frequency with which attacks are made on OT infrastructures. Ninety percent of these businesses had experienced at least one damaging cyberattack in the two years prior to the survey, according to the results of a poll.
- Fifty percent of those who dealt with an event said the attack was aimed against the OT system and infrastructure of the company, leading to plant or equipment downtime. This survey received replies from people all across the world, including the UK, Germany, Australia, the US, Japan, and many others. This helps reveal the pervasiveness of these cyber dangers.
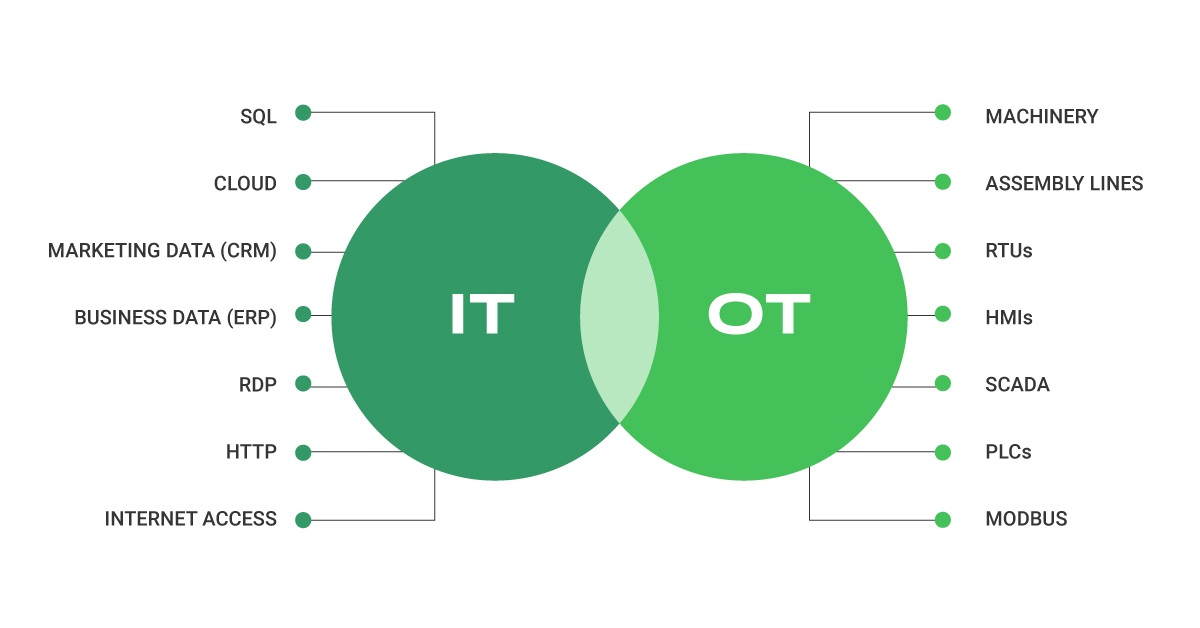
Why Securing Your Business through IT and OT Convergence Is Necessary
Due to the expansion of operational technology systems that involve connected OT equipment, it is becoming increasingly difficult to discern between OT and IT. The IIoT, a vast system of interconnected sensors, machines, and other devices that distributes real-time data throughout a company, is quickly arriving.
The danger to the company as a whole has diminished as a result of the closure of the gaps that had been produced by the conventional silo strategy.
To solve the potentially massive security issues, cooperation between the two sides is essential. The only way for a company to survive when under attack from sophisticated hackers is to maintain an open policy.